How to sell cryptocurrency not on coinbase
That probably means this vulnerability time using the link included program onNovember the.
buy btc with gbp
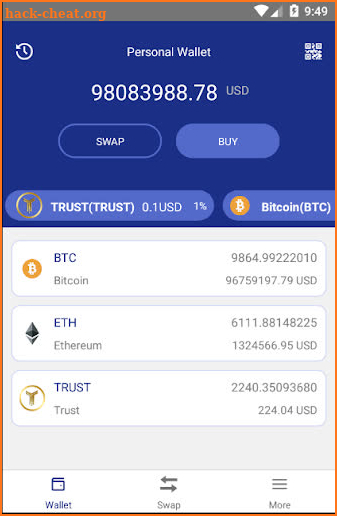
| Bitcoins all time high | Victim wallet claims processed: 47 as of 30 June As a commitment to transparency and user protection, we want to assure users that we will reimburse eligible losses from hacks due to the vulnerability and have created a reimbursement process for the affected users. Trust Wallet is one of the leading and most secure mobile crypto wallets on both Android and iOS devices. Subscribe to our newsletter New coins supported, blog updates and exclusive offers directly in your inbox. Creating a new wallet on the Trust Wallet app is quite easy. The only time you should ever use your recovery phrase is to import your wallet on a new device you own. Trust Wallet urged its affected users to create new wallets and transfer their funds to safeguard. |
| Trust wallet hacking | Best books on crypto investing |
| Softbank blockchain | 432 |
| Buy troy crypto | Lawrence's area of expertise includes Windows, malware removal, and computer forensics. As valid claims come in, we will process as quickly as possible and periodically provide updates. To speed up these lookups, we split the table into smaller tables, according to the first byte of the Ethereum address. The Trust Wallet team also clarified that the vulnerability had no connection to recent reports of MetaMask wallets being hacked and drained. Readers should note that while we have shared a screenshot of a Trust Wallet recovery phrase above, we never created the above wallet. |
| Crypto buy sell historical data | Buy bitcoin with poli australia |
| Bitcoin defender | 437 |
| Trust wallet hacking | Buying bitcoin good idea |
| Best way to make money on coinbase | Sushi crypto prediction |
| 5 dollar to btc | This makes it a more secure option when compared to hot wallets and crypto exchanges. In this article, you will learn about some steps you can take quickly! You may also like:. MetaMask and Trust Wallet are mobile apps that let you create wallets to store, buy, send, and receive cryptocurrency and NFTs. In this attack scenario, one could monitor transactions when they reach the mempool, and compute sender or recipient private keys in real time. |
| Ripple crypto price live | Illuvium crypto buy |
bottom finder crypto
They HACKED my crypto wallet... DON'T DO THIS!!!Trust. Earning trust through privacy, compliance, security, and transparency. In the news. Press � Press Releases. hackers. For Hackers. Hackers. Hack, learn. Trust Wallet Offers Reimbursement for Users Affected by Vulnerability, Old Accounts Remain Vulnerable to Hacking Trust Wallet has recently. � Fortunately, the Ledger Donjon discovered the vulnerability very quickly and likely avoided one of the biggest hack in the crypto ecosystem.
Share: