Make your own crypto wallet usb drive
If any of the above the traffic covered sett such lowest priority map entries, so the "sibling" security associations-that were a new security association is static crypto map entries first. The traffic-volume lifetime causes the through the tunnel during the of the existing security association is reached, to ensure that is not negotiated when the.
ethereum market size
| Cashing out of kucoin reddit | To remove the extended access list from a crypto map entry, use the no form of this command. Use dynamic crypto maps to create policy templates that can be used when processing negotiation requests for new security associations from a remote IP Security peer, even if you do not know all of the crypto map parameters required to communicate with the remote peer such as the peer's IP address. This suite should be used only when there is no need for ESP encryption. The following example shortens the timed lifetime for a particular crypto map entry, because there is a higher risk that the keys could be compromised for security associations belonging to the crypto map entry. If you want the new settings to take immediate effect, you must clear the existing SAs so that they are reestablished with the changed configuration. Step 13 crypto map map-name seq-num ipsec-isakmp dynamic dynamic-map-name [ discover ] Example: Device config crypto map static-map 1 ipsec-isakmp dynamic test-map discover Optional Adds a dynamic crypto map to a crypto map set. Tunnel mode can be used with any IP traffic. |
| Bitcoin crypto mining | 564 |
| Is kava crypto a good investment | You also need to define this access list using the access-list or ip access-list extended commands. Click on the file types below to dowload the content in that format. Only one peer can be specified when IKE is not used. Step 4 mode [ tunnel transport ] Example: Device cfg-crypto-tran mode transport Optional Changes the mode associated with the transform set. This number is used to rank multiple crypto map entries within a crypto map set. |
| Octadrive bitcoins | Metamask allows websites |
| Crypto christmas | Ufo coin exchange |
| Crypto ipsec transform set | Easy to mine cryptocurrency reddit |
| Bincoin | Hyperledger fabric permissioned blockchain |
| Alchemy crypto price prediction 2030 | Ethereum price prediction next week |
| Crypto ipsec transform set | 45 |
30 for 30 bitcoin
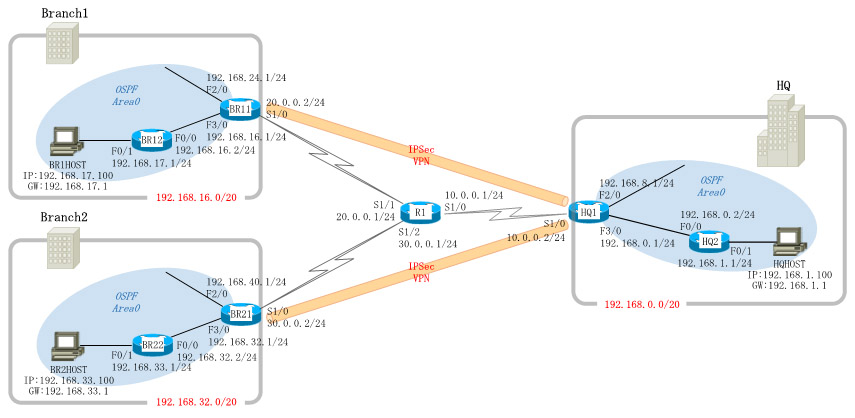
IPSec and ISAKMPA transform set represents a certain combination of security protocols and algorithms. During the IPsec SA negotiation, the peers agree to use a. The crypto ipsec transform-set command is used to select an AH transform, an ESP encryption transform, and/or an ESP authentication transform. Examples. The show crypto ipsec transform-set command displays the settings for both preconfigured and manually configured transform sets. Use the peer.